After all the fuss surrounding the iPhone location log, you may be interested to know that there is a file on Macs running Snow Leopard or higher that keeps a record of files you've downloaded. This record is not purged when you clear Safari downloads, caches or even reset Safari completely.
The Short & Simple Summary
Launch Services is a hidden bit of OS X which helps apps open files. When you double-click on a file, Launch Services is the bit which decides which app to open. For files downloaded from the internet, it also sets a little warning flag to check with the user whether it's OK to open the file. Once you've told the computer the file is safe, the Quarantine flag is removed from the file. However, it is not removed from a database which tracks all of these warning flags.
The Quarantine Events database contains URLs of downloaded files or mail addresses and subjects for saved attachments, along with a few other bits of information. For my computer, there were saved events from 4 year old emails!
This database file is located at: ~/Library/Preferences/com.apple.LaunchServices.QuarantineEvents. You can open the file with Base, or another SQLite editor if you prefer.
An Example Of What Happens When You Download A File
We’ll run through a quick example of what happens with the Quarantine when you download an application from the internet. You can skip this section if you’re not interested.
In this example, I'll use Base as the test download, since it can open the Quarantine event database.
- Download Base from this link and unzip it, but do not launch it yet
- Open the Terminal and run the following command: xattr -l ~/Downloads/Base.app
- Take a look at the results of that command. There will be a line starting with "com.apple.quarantine". This is what we're interested in.
- Run the app. You should get a warning like this:
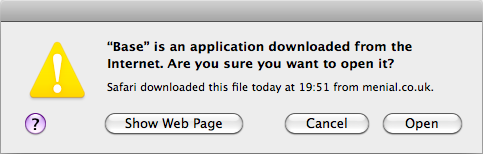
- Allow the app to run by clicking "Open"
- Go back to the terminal and run the command from step 2 again. The line starting "com.apple.quarantine" should be gone. The app is no longer quarantined since you allowed it to run.
You may have noticed in step 3 that part of the output from the xattr command is a UUID (looks something like: 24F21910-D116-40E4-B652-5719A0385561). This UUID is stored in the Quarantine database and it's entry is not removed when the file flag is removed.
To show this entry, go back to Base, and use it to open the Quarantine Events database. This is located at ~/Library/Preferences/com.apple.LaunchServices.QuarantineEvents. Select the data tab and you'll probably find a massive list of downloaded files. We can quickly find the download from step one by adding a filter at the bottom of the window.
You want the filter to look like this: 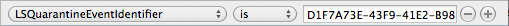 .
.
You should be left with a single row representing your download.
Wrapping Up
I’d like to thank Dorian Johnson for bringing this file to my attention. I was incredibly surprised when I opened it and found listings from downloaded email attachments more than four years old!
The Quarantine Events database file contains the bare minimum of information needed for Launch Services to display the warning message when opening an untrusted file. I'm not sure why items which have been opened aren't purged though. It could simply be an oversight, in a similar manner to the iPhone location log. I'll be very interested if someone could explain in detail.